Longtime OS X Server users were in for a shock years ago when OS X Lion Server ditched Server Admin for Server.app. One of the main features missing was any sort of firewall controls. OS X had switched from ipfw to pf and simply did not have any GUI firewall controls. Keep in mind the “firewall” option in the security system preferences is a ALF (application layer firewall) and can lock you out unintentionally for a remote Mac. It’s not meant to be a firewall for a server, but a firewall for an end user. OS X 10.10 Yosemite with Server.app version 4 now includes GUI firewall controls once again. They are located under ‘access’ in Server.app. Our VPN configuration script plus the new firewall controls can help lockdown access to a remote Mac mini in minutes.
Our automation scripts can be found on github or at code.macminivault.com. The VPN configuration script will automatically configure the a VPN tunnel with traffic (NAT) routing. To run the script paste the following command into terminal, once complete reboot. Turn off VPN and turn it back on after the reboot.
Copy and paste this into terminal on your remote Mac server:
bash <(curl -Ls http://git.io/1UlbJQ)
WARNING: Editing firewall rules can easily cause your server to be completely inaccessible. Please proceed with caution. If you are a customer of ours, we recommend touching base with our support staff before proceeding. Performing these configuration changes during our free hands on hours will ensure that we can promptly get you back online at no additional cost.
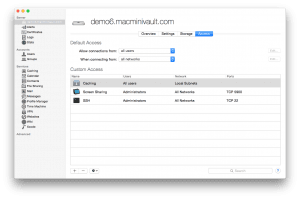
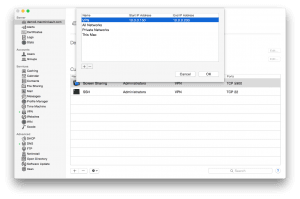
When configuring the client side be sure to edit the advanced settings and enable ‘Send all traffic over VPN connection’. After testing and confirming that VPN connectivity works and routes traffic out the external IP address of the remote Mac, we can adjust the firewall/access rules. Carefully add a new network called VPN with the IP range of 10.0.0.150 to 10.0.0.200. The gear icon on the bottom of the pane can be used to edit the networks.
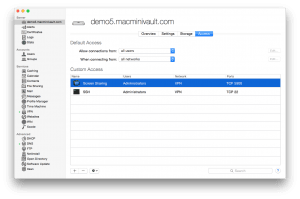
Once that is done you can change SSH and VNC to only use the VPN network. We’ll also remove caching services as we don’t want to provide caching to the local networks in the data center. The Access pane should look like this. We’ve found this configuration to work well and not cause any issues. When attempting to limit all access to the server, it can be more difficult to control access rules based on the limited GUI controls that Yosemite server currently has.
Once this current screen sharing session is closed, you will loose non-VPN access to the machine via VNC/SSH. Once connected via VPN VNC/SSH access will work when trying to connect to 10.0.0.1.
If you are a customer of ours and choose to lock down VNC/SSH access, please open a support ticket to request the IP range of our support network so we can still access the machine when support is needed.